The CA/Browser Forum, driven by industry leaders like Apple, has mandated a major policy shift in the approach to managing digital certificates that secure public-facing systems. The current 398-day lifespan for public CA-issued certificates is set to reduce to just 47 days in 2029, and the journey to get there starts in March 2026 with a 200 day validity upon renewal. Let that sink in for a second—that’s an eightfold increase in the frequency of certificate renewals.
This drastic reduction in certificate lifespan isn’t just a technical adjustment; it’s a strategic shift that redefines how we secure machine identities and machine-to-machine communication. It transforms certificates from static credentials into dynamic, high-frequency credentials that demand an entirely new operational and security model. The old “identity-as-a-perimeter” concept has evolved: identity is now the perimeter, and that perimeter will be redrawn every 47 days.
Your spreadsheets, manual renewal reminders, and ad-hoc scripts are not just inefficient; they are now an existential risk to your business both operationally and security-wise.
The New Mandate: From Operational Nightmare to Security Imperative
This accelerated timeline forces a reckoning with two unique requirements—one operational, one security—that manual processes simply cannot address at scale.
The Operational Requirement: Conquering the “Last Mile”
The 47-day mandate exposes a hard truth: getting a certificate from a Certificate Authority (CA) has never been the difficult part. The real challenge has always been the “last mile” in the renewal process: discovering every certificate, validating its ownership, renewing it, and then provisioning the new file to the correct end system and binding it to the right application.
This “last mile” is a heterogeneous mix of web servers, load balancers, application delivery controllers (ADCs), and cloud gateways. It’s a multi-vendor, multi-cloud, multi-team landscape.
When you do this once a year, you can brute-force it with manual effort. But when you must do it eight times more often, that model breaks. A single human error like a forgotten server, a mistyped command, or a failed binding doesn’t just cause a 404 error; it triggers a full-blown application outage that can cause millions in lost revenue, lost trust, and more importantly potential compromise of customer data.
At this new certificate renewal speed, automated provisioning and binding are not a luxury; they are the only critical path to operational and security compliance.
The Ownership Validation: Automating Trust
This mandate isn’t just about speed; it’s about security. A shorter lifespan radically reduces the window for attackers to exploit a compromised key. But this security benefit is not free. It is contingent on one of the most error-prone steps in the entire process: Domain Control Validation (DCV) as part of any DV, OV or EV certificates.
To compound the challenge, the DCV reuse period is also shrinking to just 10 days. That means for nearly every renewal, you must re-prove your domain ownership.
Now, think about how IT teams do this today. Someone has to respond to an email, manually upload a file to a web directory, and create a DNS TXT record. Now, imagine doing that for thousands of domains, every few weeks, without fail and any missteps. It’s an impossible operational burden and a massive security risk. If the validation step isn’t completed, the entire process grinds to a halt. You will fail compliance, risk mis-issuance, and leave your organization exposed.
AVX ONE CLM Automates Short-Lived Certificates to Meet the 47-Day Mandate
The new 47-day world demands a platform built for this next phase of certificate lifecycle management (CLM). You need a single, end-to-end, closed-loop CLM automation platform that treats certificate management as a continuous machine identity workflow it has become.
This is precisely where AppViewX provides a strategic advantage with its current capabilities and newly released enhancements.
- Solving the “Last Mile” Problem: The AVX ONE CLM platform was designed to simplify and manage the complex, heterogeneous “last mile.” It provides closed-loop automation that handles everything from request and renewal to device auto-onboarding, provisioning and even binding across your entire infrastructure—on-prem, hybrid, and multi-cloud. It doesn’t just get the certificate; it makes sure it’s working.
- Automating Domain Control Validation (DCV): The AVX ONE CLM platform automates the entire lifecycle, including the critical DCV step. By integrating with your DNS, servers, and load balancers, it can automatically perform the required validation checks, removing the human-in-the-loop bottleneck, and ensuring trust is established seamlessly and verifiably every single time.
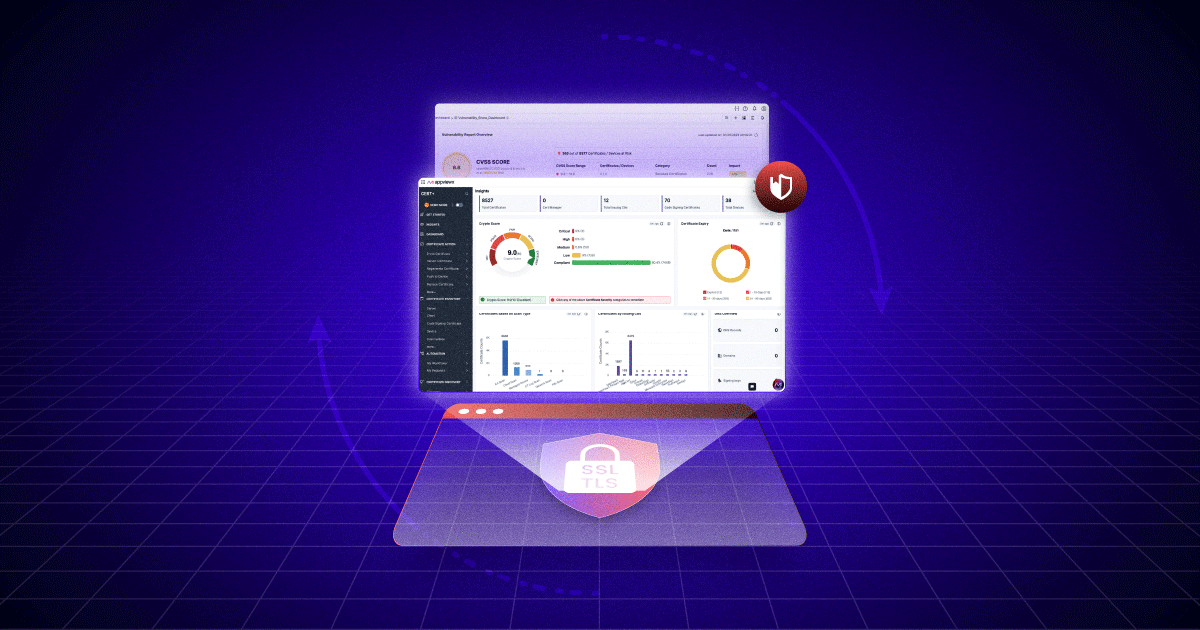
- Providing a Unified Visibility and Control Plane: In a world of multiple CAs, diverse cloud environments, and siloed global teams, AVX ONE CLM acts as a CA-agnostic, hybrid-cloud command center. It gives you a single pane of glass to discover all certificates, enforce security policies, and automate the full certificate lifecycle, regardless of where the certificate comes from or where they need to go. With the recent release version of AVX ONE CLM, IT teams can now set custom validity periods for certificates upon renewal, ensuring a smooth and accelerated path to meeting the 47-day mandate.
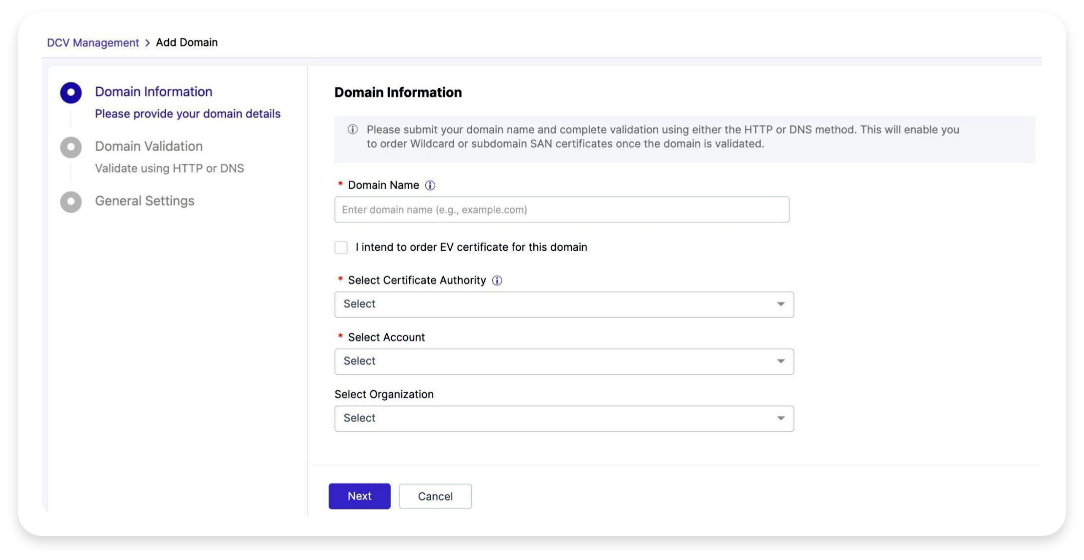 Automation of Domain Control Validation (DCV) meets the requirements of the 47-day certificate lifecycle mandate
Automation of Domain Control Validation (DCV) meets the requirements of the 47-day certificate lifecycle mandate
Key Updates to Manage Short-lived Certificates
Recent enhancements to the AVX ONE CLM platform equip organizations with powerful automation and policy controls to help them seamlessly manage and prepare for compliance with the upcoming 47-day certificate validity mandate. Enhancements include:
| Enhancement | What It Delivers | Why It Matters |
|---|---|---|
| Certificate Lifecycle & Validity | Enables definition of new certificate validity values for renewals, templated re-enrollment policies (e.g., 200-day validity), and visibility into certificates by post-renewal validity. | Helps organizations prepare for the 47-day mandate by customizing validity periods to meet CA/B Forum requirements while maintaining compliance and crypto-agility. |
| Automation of Domain Control Validation (DCV) | Automates domain discovery, monitoring, and validation for certificate issuance, including DNS record cleanup after successful validation. | Eliminates manual, error-prone domain ownership checks, ensuring faster, compliant, and reliable certificate issuance aligned with 10-day DCV reuse limits. |
| Automated Onboarding of Endpoints | Automates onboarding of servers and devices for certificate discovery and provisioning, with enhanced detection for host OS, applications, and onboarding groups. | Solves the “last-mile” challenge by ensuring certificates are properly deployed and bound across all endpoints without manual effort. |
| Renew Validity Reports | Provides visibility into certificates based on post-renewal validity and status. | Enables proactive monitoring and reporting, ensuring no certificates exceed compliance thresholds or fall out of sync with policy. |
| Re-enrollment Policy Templates | Standardizes renewals through predefined configurations such as validity periods, key strength, and algorithms. | Reduces configuration errors and ensures consistent application of enterprise-wide PKI and crypto policies. |
| Real-time Inventory and Visibility | Tracks certificate issuance, renewal, and expiration status across all endpoints and environments. | Provides operational confidence and mitigates outage risk through live compliance and expiration tracking. |
How Can I Get This?
The short-lived certificate updates are automatically available for all on-prem and SaaS AVX ONE CLM customers as part of AppViewX’s November 2025 release. With these enhancements, AppViewX customers can automate certificate renewal cycles, enforce re-enrollment policies, and turn the 47-day mandate into a strategic advantage.
If you are new to AppViewX, contact us o see how short-lived certificate updates can help you accelerate 47-day mandate compliance.
Frequently Asked Questions (FAQs)
-
What is the 47-day certificate mandate, and why does it matter now?
The CA/Browser Forum has announced that by 2029, the maximum validity for public TLS certificates will be reduced to 47 days, beginning a phased rollout in 2026 (starting with 200-day renewals).
This change will dramatically increase certificate renewal frequency and make manual management impossible. AVX ONE CLM helps enterprises prepare today by automating short-lived certificate workflows, renewals, provisioning, and validation to ensure full readiness before the mandate takes effect.
-
How does AVX ONE CLM simplify short-lived certificate renewals?
AVX ONE CLM allows admins to define custom certificate validity periods for renewals, set re-enrollment policies with standardized defaults (e.g., 200 days, RSA 2048), and automatically generate new private keys at each renewal.
This ensures certificates are continuously refreshed, compliant, and cryptographically strong—without manual intervention.
-
What role does automated Domain Control Validation (DCV) play?
For each short-lived certificate, organizations must re-validate domain ownership—sometimes as often as every 10 days. AVX ONE CLM automates DCV by discovering domains, performing DNS or file-based validations, and cleaning up DNS records after successful validation.
This automation eliminates human error, reduces issuance delays, and ensures continuous compliance with CA/B Forum requirements.
-
How does automated onboarding of endpoints help with SLC management?
Automated onboarding enables AVX ONE CLM to discover and provision certificates directly to servers, devices, and applications without manual setup. The platform detects host OS and applications, applies onboarding policies, and supports major systems such as Linux, Windows, F5, Apache, Tomcat, and Nginx.
This eliminates the “last-mile” challenge of certificate deployment and ensures every endpoint remains continuously trusted.
-
How do these new features improve security and operational efficiency?
By automating certificate validity management, domain validation, and endpoint onboarding, AVX ONE CLM removes the risk of missed renewals and expired certificates—common causes of costly outages.
It also enforces consistent crypto policies, reduces the attack surface through frequent key rotation, and provides full visibility into certificate health and compliance across hybrid, multi-cloud environments.
Ready to take the first step toward 47-day compliance? Visit the 47-Day TLS Solution Page